The digital landscape of modern journalism is fraught with peril, a reality underscored by the recent experience of ProPublica investigative reporter Robert Faturechi, who found himself at the center of a sophisticated online impersonation campaign. These incidents, involving attempts to extract sensitive information from international contacts by masquerading as Faturechi, highlight a disturbing evolution in cyber deception, posing significant challenges to journalistic integrity, source security, and the broader ecosystem of secure digital communication. The incidents, unfolding across platforms like WhatsApp and Signal, point towards a concerted effort to weaponize trust, a cornerstone of investigative reporting, for potentially nefarious purposes extending beyond simple financial fraud.
A Reporter’s Unsettling Discovery: The Canadian Connection
The first alarm sounded for Faturechi with an unexpected call from an unrecognized Canadian number. On the other end, a voice identifying himself as a Canadian military official posed a disquieting question: had Faturechi been attempting to contact him on WhatsApp, seeking information? As an investigative journalist, Faturechi routinely engages with a wide array of sources, yet this particular inquiry drew a blank. He could recall no recent attempts to cultivate sources within the Canadian military. The official’s subsequent warning crystallized the gravity of the situation: "It seems as though someone is impersonating you."
Faturechi, grappling with the surreal revelation of a "Fake Me," immediately faced a cascade of questions: What was the impostor seeking? Were they merely using his name, or had they replicated his professional identity, including his photograph? A critical journalistic instinct also surfaced: how could he verify the authenticity of this warning, ensuring the Canadian official himself wasn’t part of a more elaborate deception? The official, understanding the reporter’s skepticism, promptly offered to send an email from his government account to confirm his identity, complete with screenshots of his WhatsApp exchange with the impostor. This act of transparency provided the necessary assurance, allowing Faturechi to grasp the scope of the emerging threat.
The screenshots, upon receipt, painted a clearer picture: the impostor was using a Miami phone number and Faturechi’s official ProPublica headshot as their WhatsApp profile picture. The messages themselves were direct, "This is Robert Faturechi from ProPublica," Fake Me wrote, "I really need to get in touch with you." The Canadian official, whose work involved dealings with various countries, including Ukraine, requested discretion regarding the specifics of his role. This detail, however, offered an initial clue into the impostor’s potential targets and motivations. ProPublica’s security team was immediately alerted, but the immediate actionable advice was limited to reporting the fraudulent WhatsApp account. Faturechi filed the report and attempted to put the unsettling incident behind him.
The Latvian Link: An Escalation of Tactics
The respite was short-lived. Just two weeks later, a second, more alarming incident unfolded, indicating a pattern rather than an isolated event. This time, the warning came from a Latvian businessman, a figure involved in providing equipment to the Ukrainian military and collaborating on drone development projects with Ukrainian forces. The Latvian reached out to Faturechi on LinkedIn with a seemingly innocuous message: "Hey! Was good to chat on Signal! Let’s connect here as well!" The crucial detail, however, was that Faturechi had never communicated with the businessman on Signal, the highly encrypted messaging application.
The Latvian’s proactive approach stemmed from growing suspicion. He, too, had received messages from someone using Faturechi’s headshot and claiming to be him on Signal. The impostor’s questions were pointed: "Am I right in understanding that you are an expert in the field of UAVs?" referring to Unmanned Aerial Vehicles, or drones. Fake Me elaborated, "My clients are particularly interested in the application of UAVs in Ukraine." The Latvian, initially engaging, offered to discuss the matter via a phone call. However, Fake Me demurred, stating discomfort with phone conversations and preferring "written format" or "voice messages." This reluctance to engage verbally is a classic red flag in impersonation scams, often used to avoid detection through voice recognition or to maintain anonymity.
As the Latvian’s suspicions deepened, he insisted on a video call. The impostor, seemingly relenting, then sent what appeared to be step-by-step instructions for a secure video chat. These instructions, however, were a sophisticated ruse designed to trick the Latvian into compromising his email account access. Recognizing the malicious intent, the Latvian businessman promptly blocked the impostor, narrowly avoiding a potentially damaging security breach. These consecutive incidents revealed a calculated and persistent campaign, not merely random phishing attempts, but targeted social engineering aimed at individuals with connections to sensitive geopolitical matters.
The Broader Threat Landscape: Impersonation as a Tool of Deception

These impersonation attempts against Faturechi are not isolated incidents but rather symptomatic of a growing and increasingly sophisticated online threat landscape. Cybercriminals and potentially state-sponsored actors are continuously evolving their tactics, exploiting human trust and the inherent anonymity of the internet. Impersonating a journalist, in particular, is a potent strategy. Journalists, especially investigative reporters, cultivate relationships based on trust and often seek information on sensitive topics, making their identity a valuable asset for those looking to covertly gather intelligence or manipulate narratives.
The motivations behind such impersonations can vary. While some online deceptions, like the notorious "pig butchering" scams chronicled by ProPublica itself, are purely financially driven, others aim for intelligence gathering or disruption. The "pig butchering" phenomenon, often linked to human trafficking in Asia, forces victims to engage in long-term emotional manipulation to extract vast sums of money. Faturechi’s case, however, displayed no overt requests for money or gift cards, suggesting a different objective: the theft of sensitive information, reconnaissance, or perhaps even disinformation campaigns.
The history of high-profile phishing attacks serves as a stark reminder of the potential impact. John Podesta, chairman of Hillary Clinton’s 2016 presidential campaign, famously fell victim to a spear-phishing email disguised as a Google security alert. This breach granted hackers access to his personal Gmail account, leading to the public release of thousands of emails that significantly impacted the election. This incident underscored that even sophisticated actors can be ensnared by well-crafted social engineering tactics.
Why Journalists are Prime Targets and the Geopolitical Context
Investigative journalists operate at the nexus of power and public interest, often uncovering uncomfortable truths that powerful entities wish to keep hidden. This role inherently places them in a vulnerable position. Sources, who often take significant personal risks to share information, rely on the journalist’s integrity and ability to protect their identity. When a journalist’s identity is compromised, it erodes this critical trust, potentially chilling future whistleblowing and making it exponentially harder to pursue vital stories.
The specific targeting of individuals connected to the Ukrainian military and drone development, as seen in Faturechi’s case, strongly suggests a geopolitical dimension. With the ongoing conflict in Ukraine, information related to military aid, equipment, and strategic partnerships is highly valuable to various state and non-state actors. Impersonating a ProPublica journalist, known for rigorous reporting, lends a veneer of credibility that could persuade unsuspecting individuals to divulge information they would otherwise safeguard. This makes the impersonation not just a personal inconvenience but a potential national security concern, as it could compromise military intelligence, supply chains, or diplomatic efforts.
Challenges for Secure Messaging Platforms: Privacy vs. Policing
The incidents involving WhatsApp and Signal highlight a fundamental tension within secure messaging platforms: the balance between user privacy and the ability to police malicious activity. Both platforms are lauded for their robust end-to-end encryption, which ensures that only the sender and intended recipient can read messages, not even the platform itself. This "privacy by design" is crucial for journalists, activists, and anyone needing secure communication, as it minimizes metadata collection and prevents third-party eavesdropping.
However, this very design makes combating impersonation and other scams incredibly challenging. Signal, for instance, collects minimal user data – primarily account creation time and phone number – and stores nothing about message content or who users are messaging. This commitment to privacy, while foundational to its appeal, means Signal has limited tools to detect or prevent sophisticated social engineering attacks. Red flags, such as suspicious links within messages, are not detectable by Signal without compromising its encryption protocols.
WhatsApp, while part of a larger corporate entity (Meta), also employs end-to-end encryption. A spokesperson for WhatsApp stated that the company has a "strong track record of banning those trying to scam others and staying ahead of scammers and their tactics," and took "appropriate action" against the account impersonating Faturechi. However, like Signal, WhatsApp cannot see the content of encrypted messages unless a user reports them. While it has the technical ability to see who its users are messaging, a spokesperson indicated it’s rare for the company to store that data. WhatsApp primarily relies on monitoring suspicious behavioral patterns, such as attempting to launch many accounts from a single location, to preemptively identify and ban scam accounts.
Experts like Cooper Quintin, a technologist at the Electronic Frontier Foundation (EFF), acknowledge the rising trend of scams on secure messaging apps. While Signal has implemented measures like slowing down spammers and making links from unknown senders unclickable, there are inherent limits to what can be done without eroding the privacy protections that define the platform. Quintin himself insisted on a video chat with Faturechi to verify his identity, underscoring the pervasive nature of digital mistrust.

Runa Sandvik, a digital security expert consulting for ProPublica, points out the impracticality of implementing verification systems, akin to those on Facebook or Instagram, for platforms like Signal. Signal is run by a small nonprofit, lacking the resources for such extensive verification, which would also necessitate collecting more user data, directly contradicting its privacy ethos.
Official Warnings and Broader Implications
The impersonation of journalists is not an isolated phenomenon affecting only Faturechi. Other prominent news organizations have reported similar incidents. The New York Times recently flagged an X (formerly Twitter) account falsely claiming to be an intern. In 2023, Reuters reported that two of its reporters in China were impersonated on Instagram and Telegram, attempting to gather information on activists protesting COVID-19 policies. A Reuters correspondent in Saudi Arabia also warned followers about an impostor on WhatsApp. These cases illustrate a concerted effort by various actors to exploit journalistic identities for information gathering or disruption.
More alarmingly, government entities have issued warnings about state-sponsored campaigns. The German government recently issued a vague but serious alert regarding a likely state-sponsored actor attempting to hijack Signal accounts of government officials and journalists across Europe. In a particularly chilling revelation, the FBI announced last month that individuals associated with Russian intelligence were posing as Signal’s security department to trick American government officials and journalists into providing information that would grant hackers control over their accounts. Once compromised, these accounts could expose conversations, contact lists, and allow the perpetrators to send messages as the victim, potentially sowing disinformation or compromising national security.
The implications for investigative journalism are profound. The foundation of this work rests on courageous individuals who trust journalists with sensitive information, often at great personal risk. If potential sources cannot be sure of a reporter’s identity, this crucial relationship of trust is shattered, making them far less likely to come forward. This erosion of trust, coupled with increasing attacks on media credibility, creates a hostile environment for essential public interest reporting.
Mitigation Strategies and the Call for Vigilance
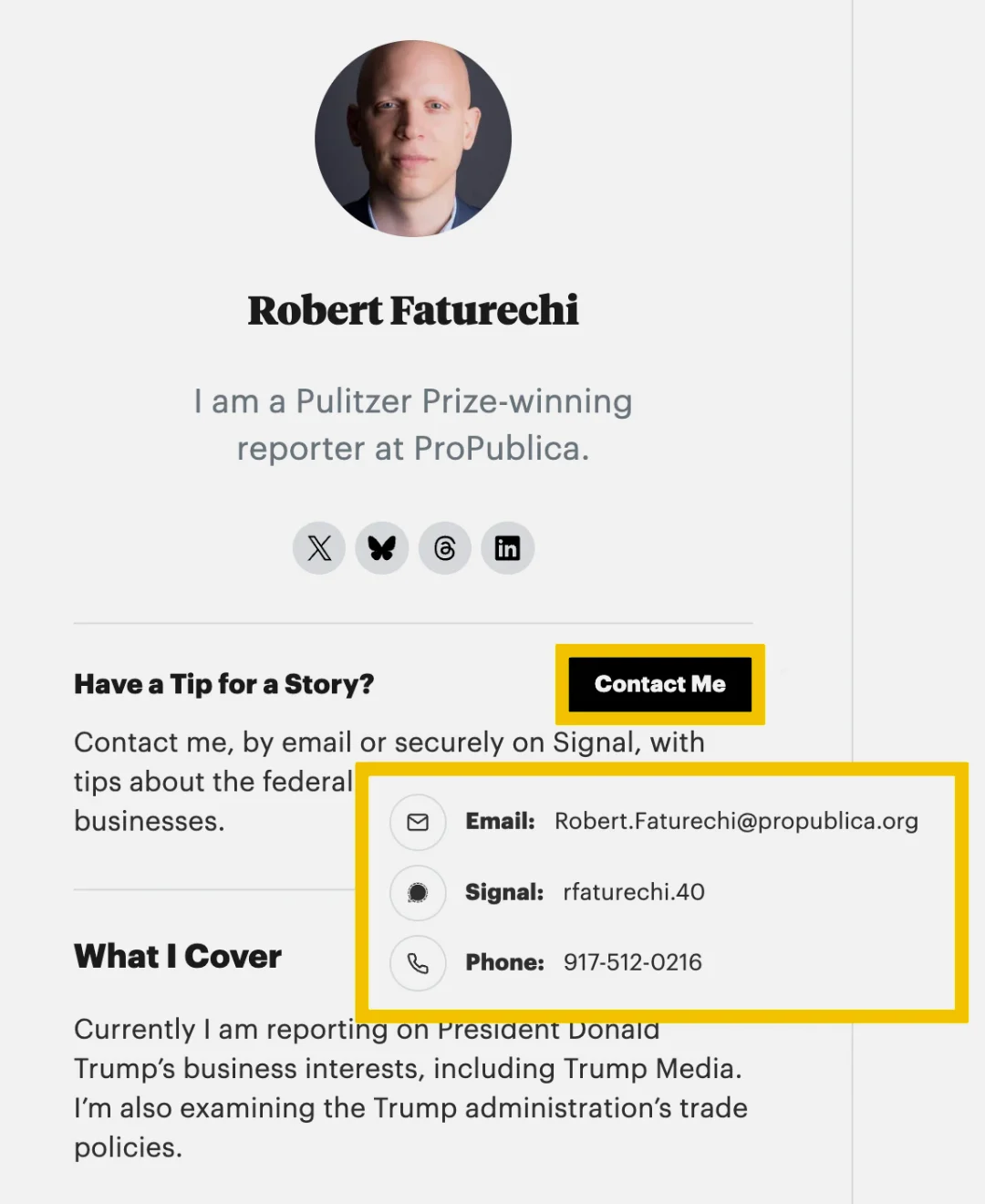
In this evolving landscape of digital deception, vigilance and proactive verification are paramount. For individuals contacted by someone claiming to be a journalist, the most effective defense is to conduct a "little reporting of your own." ProPublica, recognizing this need, ensures that every reporter has a public bio page with verified contact information, including Signal handles and official @propublica.org email addresses. This allows potential sources to cross-reference contact details and confirm identity.
This principle extends to all reputable news outlets. If a journalist reaches out, verify their identity through their organization’s official website or established social media channels. Check for consistent email domains, verified social media accounts, and cross-reference phone numbers or Signal usernames against publicly available professional profiles.
Experts like Runa Sandvik emphasize the importance of transparency from journalists themselves. When impersonation occurs, silence is not an option. Being "very public about it" and letting people know "this is happening" serves as a crucial warning system, raising awareness and equipping potential targets with the knowledge to identify and thwart similar scams.
The incidents involving Robert Faturechi serve as a stark reminder that the digital battleground is expanding, with trust itself becoming a weapon. As technology advances, so too do the methods of deception. Protecting the integrity of journalism and the security of its sources requires a collective effort: robust platform security, vigilant users, and transparent reporting of threats. In an era where information is power, ensuring the authenticity of those who seek and disseminate it is more critical than ever.